Photo credit: Roobcio/Getty Images
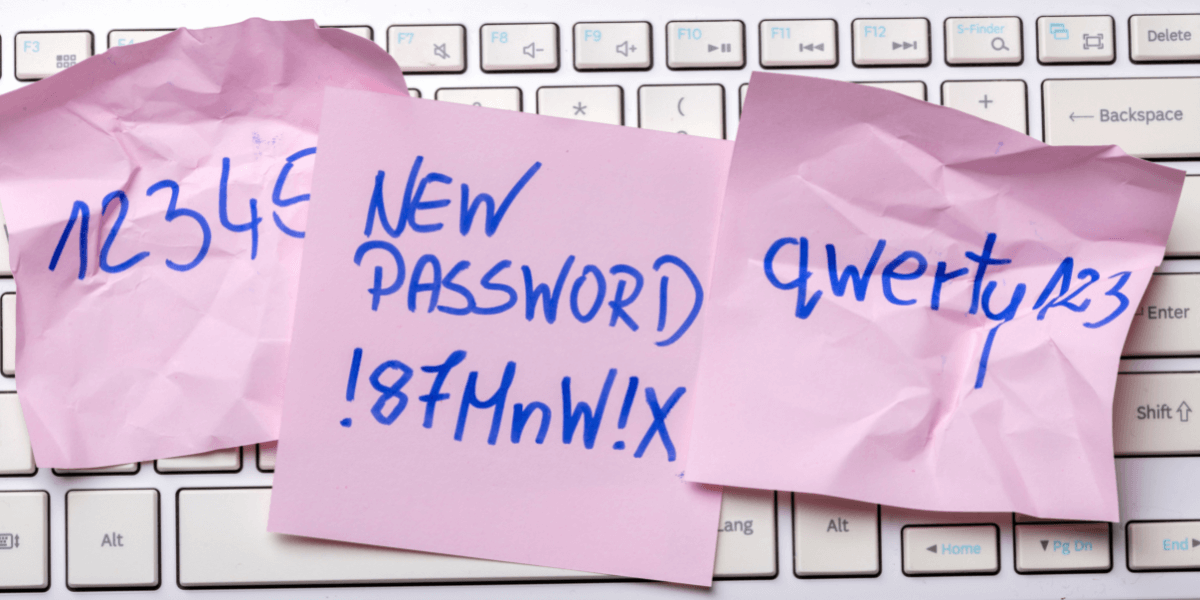
On December 22, 2022, popular password manager LastPass delivered a hunk of coal to its 30 million users: their sensitive information had been compromised in a security breach.
Password managers, such as LastPass, are services that allow users to generate and store unique passwords for their online accounts. Rather than using the same password for multiple accounts or using weak passwords, password managers allow users to create complex passwords for each of their accounts and store them in a secure, encrypted format. Using one “master password,” a user can automatically log into accounts without having to rely on their own memory.
Users’ memory (or lack thereof) is an important factor in password security, and for nearly a decade Jelena Mirkovic, Project Leader at USC’s Information Sciences Institute (ISI), and her team have studied the memorability and security of passwords, and the way in which these two characteristics are at odds with each other.
Relying on one’s memory is what tends to make passwords less secure. Mirkovic and her team have found that users usually take one of two approaches to create a password they can remember. One method is to make a weak password using personal facts (i.e. names and birth dates) that make it easy to remember, but also easy to guess by a hacker. The other common method is to create a long, complex, relatively secure password, but then use it on a number of different sites, making it less secure because it just takes the breach of one site for the password to become compromised.
Through their research, Mirkovic’s team found that users value memorability over security. So they’ve set out to develop methods that help users create passwords that are both memorable and secure.
Start with Memorability
Mirkovic and her team started this research in 2014. At that time, said Mirkovic, “researchers had been working on passwords, and the research was prolific. Every conference had a few papers on either a new way to do passwords, or how to measure the strength of passwords, and I thought that we should look at it from a different angle. People had focused a lot on trying to make passwords secure and strong, and less on the memorability of passwords.
She continued, “So we started our research a little backwards. We started by saying ‘we think memorability is important, let’s see how we can improve it.’
Life Experience Passwords (LEPs)
Working with cognitive scientists and language experts, Mirkovic and her team set out to create an automated authentication process that relied on a user’s existing memories.
“The hope was that if we asked people about something that was already in their mind – like a past memory of an event – then memorability would be a given because they already remember it. So we just needed to find a way to elicit those memories in a way that was consistent enough to build a password.
They ended up with LEPs, a cross between traditional passwords and security questions. Typically, security questions ask the same things, which can make them easy to guess by hackers. For example, said Mirkovic, “they ask the name of your favorite teacher. With a dictionary of names a hacker can easily get that.”
Her team asked for several facts about an event chosen by the user. “So if they chose a trip, we would ask: ‘where did you go? Who did you go with? When did you go?’ and so on.
The team transformed these existing memories into a series of questions and answers. The questions were used at authentication time as hints for the user, and the answers became the password.
The results were outstanding. The team found that LEPs had two to three times higher recall than regular passwords and they are many orders of magnitude stronger than an ideal, random, eight-character password. The one drawback, however, is the amount of time required by the user.
“For a user, instead of just typing the password it would take them three to five times that amount of time because they are answering multiple questions. So we realized that LEPs are maybe best for protecting very important accounts where you can ask additional questions, and where the user is willing to put in that effort.”
Mnemonics Passwords (MNPass)
According to Mirkovic, “the question-answer format worked well, but it required some effort from the user. So we thought, ‘let’s see if we can make this work with regular passwords,’ which are just one phrase or one long word.”
“We really departed from the notion of ‘give us a blend of uppercase and lowercase and special characters and digits’ because you just end up with a really complex string of characters that is not memorable.
Her work with cognitive scientists showed that people remember the important things, but they don’t remember details. “So it’s really hard for them to remember, for example, which special character they put where because it’s such an insignificant detail” said Mirkovic.
Focusing on memorability, the team incorporated mnemonics. A mnemonic is a way of remembering something using a pattern of letters or images.
In this authentication method, called MNPass, the researchers used a series of letters as prompts to users, and users would come up with the words that they associated with those letters. This string of words would then become the stored password. The next time the user logged in, they would be given those same letters as cues.
Some of the words users chose were too common, and could easily be guessed by hackers. Mirkovic had a plan for that: “The second thing we tried was suggesting one of the words. So one of the words would become quite long and rare. For example, let’s say that the letter prompt was M, instead of May, it would suggest meningitis, or something a little longer and less common. And then we would let users choose the rest.
With the incorporation of this additional method, the team found that memorability was not impacted but security increased
The MNPass authentication hits increased recall of passphrases by 30–36% after three days, and by 51–74% after seven days.
GuidedPass
With the focus remaining on memorability, Mirkovic’s team looked at other ways to allow users to create something memorable, while guiding them towards password strength.
In their most recent project, the team designed a system that suggests real-time password modifications to users. The modifications preserve the password’s semantic structure, thereby maintaining its memorability, while increasing its strength.
“The user would choose a passphrase, which is longer than the password, and usually it’s a sentence or several words. We would analyze the security of it using natural language processing tools, and then we would make suggestions on how to make it stronger.”
An example? “Let’s say that a passphrase was ‘apples start growing on trees, and I like red.’ We might say: ‘You need to make this stronger. These are all common words. Try inserting a number in the middle, or instead of ‘apple’ try selecting a less common word. And we would provide several suggestions, but we would let the user choose what makes sense, because it needs to be memorable to them.” said Mirkovic.
The team found that GuidedPass outperformed competing approaches both in password strength and in recall performance
Password Managers of the Future
Mirkovic’s upcoming work involves researching whether it is possible to have a password manager that does not store passwords, but generates passwords. She offered an example of what she hopes to create:
“If I’m trying to log into email, then I would input my master password and a cue (e.g., “email” or “Outlook”) and a password would be generated. I could literally have a piece of code on my laptop or phone that would generate it. It’s just like a calculator calculates something, but doesn’t remember any of my inputs.”
But in the meantime, she still highly recommends traditional password managers, even in light of the recent LastPass breach, saying, “The LastPass security breach should not discourage users from using password managers, since they vastly increase the security of passwords.”
Mirkovic continued, “Because systems and software are very complex today, it is not unexpected that any online business can suffer a breach. In those cases, a quick response and a quick, honest information being communicated to users can make a big difference, followed by actions that fix the cause of the breach. LastPass seems to have had a reasonably secure way to store user passwords (encrypted in a vault), so I think they are still OK to be trusted by users.”
Tips from a Password Pro
After years of studying passwords, security and memorability, Mirkovic had some suggestions regarding passwords. As mentioned up top, she remains a proponent of password managers.
- Accept random passwords if your password manager suggests them, otherwise come up with a random password yourself, the manager will remember it.
- For passwords that you need to remember, choose a long password. This can be multiple words, a phrase, etc. Mirkovic usually uses five to seven words and preferably a mix of languages or a non-expected language (e.g., if the site is in English use non-English words).
- If passphrases are long enough, you don’t increase security or strength much by adding numbers or special characters.
Published on January 23rd, 2023
Last updated on May 16th, 2024