Members of MagicWire present their project at the Hacking for Defense showcase Photo/Nicolas Sage
At the beginning of their Hacking for Defense, or H4D, class this spring, William “Walker” Pollard and his four teammates in MagicWire were given a tough problem: how might U.S. Air Force personnel predict and prevent cyberattacks that could devastate their bases’ energy supplies?
The challenge, devised by the Air Force Office of Energy Assurance (OEA), immediately appealed to the engineer in Pollard, a USC Viterbi graduate student in computer science. He wanted to “dive right in,” attack the issue, and use it as the foundation for a potential deep technology startup.
One of the U.S. Department of Defense’s (DoD) goals in promoting the H4D course is to teach students like Pollard to step back and reframe real-world problems through in-depth interviews and hands-on experimentation, after which students can suggest approaches to meaningful technological solutions addressing military needs.
A Class Bridging the Gap Between the Military and Elite Students
The DoD H4D course is taught at several universities across the country, including Stanford and Georgetown, but rarely has it been connected to a university’s own defense innovation initiatives.
At USC, H4D is part of Project PALISADES (Promote, Accelerate, and Launch Innovation in the Security, Aerospace, and DEfense Sectors), an initiative of the USC Viterbi Office of Technology Innovation and Entrepreneurship linking the Silicon Beach, military, and aerospace communities. The course is linked to the efforts of the National Science Foundation (NSF) Innovation Corps (“I-Corps”) program supporting technology translation to the marketplace.
“USC is committed to supporting security needs with Silicon Beach approaches and world-class technical solutions,” said Andrea Belz, USC Viterbi’s vice dean for Technology Innovation and Entrepreneurship. “We are excited to participate in this DoD initiative.”
Added Matt Gratias, Pacific Regional director of MD5, DoD’s National Security Technology Accelerator, which supports the course: “Hacking for Defense allows top students, who would not typically come into contact with the military, to interact with them and bring outside the box thinking to bear on important problems.”
Gratias co-taught USC’s Hacking for Defense class with Clifford Neuman, director of USC’s Center for Computer Systems Security, a scientist at the Information Sciences Institute, associate director of the Informatics Program, and USC Viterbi associate professor of computer science practice; and Farzin Samadani, a national I-Corps instructor from the NSF-backed Innovation Node-Los Angeles. In the course, the trio discussed fundraising, business models, doing business with DoD, solution architectures, and the importance of interviewing experts in the marketplace.
The team was joined by US Army Lt. Col. Ashok Deb, a computer science Ph,D. student working at ISI who served as a teaching assistant and military expert.
Based on the I-Corps “Lean Startup” approach to entrepreneurship, the course teaches students to quickly pivot and change coure based on new information.
“Students are learning how to frame a problem that needs solving, rather than searching for a problem that fits solutions already in their arsenal,” Neuman said.
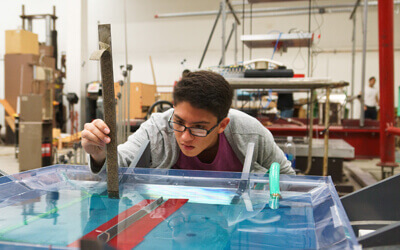
Eighteen students – 12 from USC Viterbi, two from the USC Marshall School of Business, two from USC Dana and David Dornsife College of Letters, Arts and Sciences, and two from USC Jimmy Iovine and Andre Young Academy – comprised four interdisciplinary teams. The end goal: create a minimally viable product concept that could one day possibly be transformed into a commercial product.

General David H. Petraeus Photo/Nicolas Sage
On Thursday, April 19, the teams, including MagicWire, made presentations at USC’s inaugural H4D showcase. Audience members included retired General David H. Petraeus, a USC Judge Widney Professor; retired Lieutenant General Jeffrey W. Talley, a professor of practice at USC Viterbi and the USC Price School of Public Policy; several angel investors; senior military leaders; and other members of the Southern California aerospace and defense community.
“Just the ability of these students to distill complex problems and work through the issues of solving them impresses me,” General Petraeus said.
Innovative Approaches to DoD’s Vexing Problems
The presenting teams included:
MagicWire – Providing a secure communications channel between utility companies and renewable energy sources, such as solar power, at Air Force bases. Problem Sponsor: Air Force Office of Energy Assurance (OEA)
Turnstone – Empowering digital counter-terrorism messaging teams in their efforts to challenge extremist narratives online. Problem Sponsor: U.S. Department of State
Team Queue – Through facial recognition and undercarriage sensors, among other technologies, helping military base guards quickly decide who should and should not be permitted to enter the base in a vehicle. Problem Sponsor: Engineering Research and Development Center of the U.S. Army
Ready, Patient One – Developing a way for surgeons transporting disaster patients by plane to find hospitals on the ground that can quickly provide robust medical for scores of victims. Problem Sponsor: U.S. Air Force, 18th Air Force Air Mobility Command
“This class not only helped me learn valuable career skills like public speaking, interview etiquette and startup planning but also offered our team the prospect of turning our project into an actual product,” MagicWire’s Pollard said.
Added Mimi Tran Zambetti, a sophomore at the USC Iovine and Young Academy and member of the Turnstone team: “H4D has been one of the greatest learning experiences I’ve had so far. I believe that H4D is one of the best models for project-based classes out there. The secret sauce is giving students a problem-sponsor to work with, so that they’re solving a real problem out there, which is much more compelling than a regular class project.”
MagicWire Meets with the Air Force
Over the course of 15 weeks, Pollard and his MagicWire teammates conducted over 90 interviews, including with high-ranking officials at Edwards Air Force Base and the Los Angeles Department of Water and Power. They also met with Roger Schell, a renowned computer security expert and technologist.
As part of H4D, they worked closely with Eric Griesenbrock, MagicWire’s adviser and the director of innovation and strategic integration at the Air Force OEA. Griesenbrock spoke with team members weekly, gave them advice and helped facilitate interviews with military personnel.
In time, team MagicWire reframed its problem to providing a secure communications channel between utility companies and renewable energy sources, such as solar power, at Air Force bases. So compelling was the team’s analysis that MagicWire was invited to participate in a DoD hackathon at the University of Colorado Boulder, where the team successfully demonstrated its technology.
On April 10, the five members of MagicWire flew to Washington D.C. to brief Frank Konieczny, the U.S. Air Force’s chief technology officer, and Peter Kim, the Air Force’s chief information security officer, about their progress. At the Pentagon, Konieczny and Kim reacted enthusiastically to the hour-and-a-half presentation, said Robert O’Dowd, a MagicWire member and USC Marshall School of Business student.
“It was the strongest validation for us that what we were doing was the right thing,” he said.
Although the semester has just ended, team MagicWire plans to continue working on its technology. They were selected as finalists to participate in a special MD5 event in San Francisco, where they will pitch its project to venture capitalists from Founders Fund, other venture funds, and a group of special government agencies charged with supporting venture formation.
“We want to see where this will take us,” Pollard said.
Published on May 24th, 2018
Last updated on March 31st, 2022