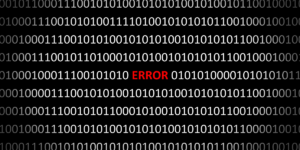
Trojan research team recognized for their work developing a novel cybersecurity tool (Image Credit: iStock)
With 5.3 billion smartphone users worldwide, it’s no surprise that the mobile app market is booming. According to Tech Crunch, in 2020 alone, 218 billion apps were downloaded, including apps that store personal information such as our passwords, fingerprints, face IDs, and more. As a result, it’s imperative that the data collected by these apps is kept safe.
That’s why researchers at USC Viterbi’s Department of Computer Science have developed a tool for ensuring app data security.
Yingjun Lyu and Sasha Volokh, former and current computer science Ph.D. students respectively, along with their advisor, Associate Professor of Computer Science William G.J. Halfond, developed the tool named SAND. Their paper, “SAND: A Static Analysis Approach for Detecting SQL Antipatterns,” won an ACM Distinguished Paper Award at the 2021 ACM International Symposium on Software Testing and Analysis (ISSTA).
Lyu, who graduated in 2019, described SAND as a defense against “injection attacks.” Injection attacks occur when an attacker enters malicious input into a program, negatively altering its behavior. To explain this concept, Lyu used an example of a database that stores students’ grades.
“Let’s say we want to search for a student’s grade—perhaps the student is supposed to input their name, and the program searches its databases for their name to return their grade,” said Lyu, who now works for Amazon Web Services. “However, if the user successfully injects an SQL statement in the input bar, all the data in the table becomes corrupted.”
This type of attack is a major problem in mobile security and is considered one of the top 10 app security risks for developers, according to the Open Web Application Security Project. It can corrupt locally stored data in an application, severely impairing a user’s app experience.
Enter SAND, which analyzes the SQL databases in applications and detects any sort of unusual pattern.
Usually, a mobile application’s creator or owner has permission to access all the code in the program. So, SAND can be executed by this individual to “quality check” the program before deployment. It essentially traverses the program’s code and alerts the developer about potential “problem areas” that can lead to an attack before it happens.
“Finding injection vulnerabilities in code is very hard for developers to do, since it requires a lot of analysis infrastructure,” said Halfond. “SAND provides a ready-made analysis infrastructure to developers that allows them to more easily and effectively find these vulnerabilities and improve the security of their code.”
Published on March 29th, 2022
Last updated on March 29th, 2022